The hallmark of the Visory experience, our dedicated team of professionals provides a high degree of support for all your IT needs
Leading edge solutions that are always working to maintain the integrity of your firm’s IT backbone
Best in class security to protect your firm’s data and technology
Tips, advice, and industry insight from our team of accountants and business owners to yours.
Bypass the wait time and access Visory’s Obsessive Client Support®
Take your business to new heights with Visory’s flexible QuickBooks hosting solutions
The same Sage you work in every day, only better
An affordable CRM for small- and medium-sized businesses, built to support your sales, marketing and customer service needs
Revolutionize your next tax season with added efficiency and mobility
Access critical applications that are integrated seamlessly into your workflow, conveniently hosted on the same server
Access affordable enterprise-grade hosting solutions with none of the IT burden

We’ll help you develop and implement the right cybersecurity policies and protocols to keep your firm secure and in compliance with regulatory guidance
We’re here to manage your firm’s IT activity, safeguarding the integrity of your infrastructure and devices, so you don’t have to
Our dedicated professionals can be your outsourced IT team, so your internal resources don’t have to bear the burden of uptime alone.
We’ll manage your cybersecurity policies and protocols to keep your firm secure and in compliance
Security that ensures everyone granted access is who they claim to be
Educate and train your most important last line of defense – your people
Protection where people and their machines intersect
Secure access to your data. Reduce the risk of compromise, prevent cyberthreats.
A different approach to protecting emails
Secure single sign-on access for a connected world
Backup your data for business continuity and compliance
Keep everyone on the same page. Any user, every device.
Secure connections for all your users, devices and networks
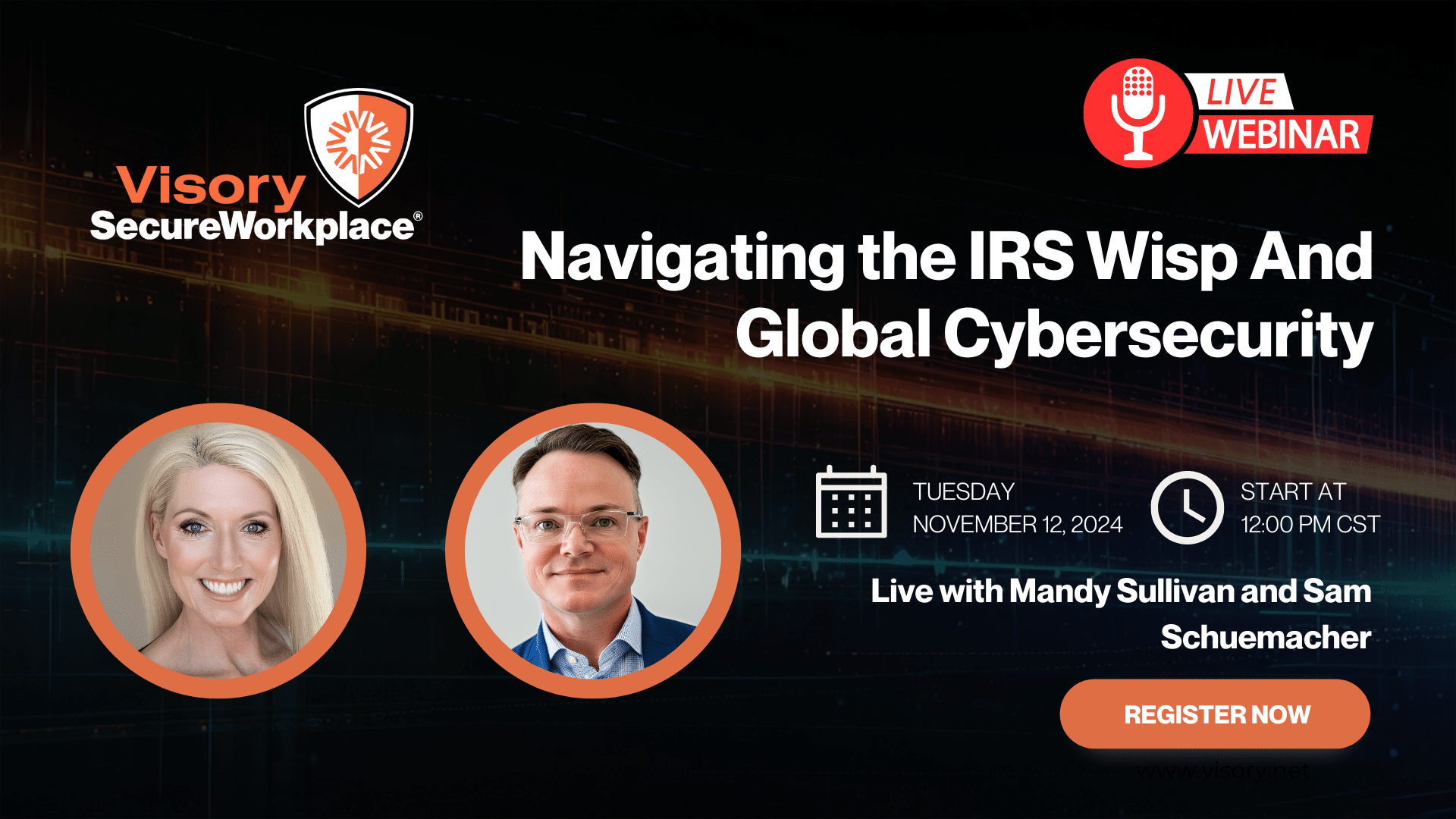
Get started on a robust security plan with a WISP for your business
Protect your organization with the expertise of our Chief Information Security Officers (CISO) without having to hire a full-time resource

IRS 4557 and the FTC Safeguards Rule
Complying with state and federal privacy regulations and more
Get started on a robust security plan with a WISP for your business
Educate and train your most important last line of defense — your people.
Protect your organization with the expertise of our Chief Information Security Officers (CISO) without having to hire a full-time resource
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
The biggest stumbling block for registered investment advisors when it comes to guarding against cybersecurity breaches is not technology-based, it’s a people problem. The right technology is critical, but RIA leaders can face a bigger challenge in fostering a cybersecurity-sensitive culture in a way that resonates throughout all levels of their firms.
RIA technology policies should be non-negotiable, but the reality is, today’s work force tends to need convincing about how these protocols benefit and protect them, their employers and their clients from cyberattacks. Generation X and millennials in particular place a higher premium on convenience versus privacy.
With rare exception, no advisor or RIA employee intends to put client data or firm assets at risk by not adhering to firm policies on cybersecurity. But cyberthieves are increasing in their sophistication, making compliance with these policies a necessity. There was a new identity fraud victim every two seconds in 2014 — that’s $16 billion stolen from 12.7 million U.S. customers — according to Javelin Strategy & Research’s 2015 Identity Fraud Study.
Firms are best served when the senior leadership explains why their cybersecurity policies exist and deliberately models appropriate behavior. When the top levels of the RIA lead by example, cybersecure behavior and attitudes become “normalized” and compliance is much easier to come by.
RIA owners wondering how to start building a cybersecure culture can lead by example with the following:
- Formally review the firm’s technology policies regularly. Most RIAs insist that those new to the firm read, review and sign the firm’s documented policies on technology usage and security. Requiring everyone to revisit and re-sign technology policy documents at least annually is a reminder to advisors and staffers about the importance of compliance.
- Circulate outside news about cyberattacks. Share the latest headline news on cybersecurity breaches with your colleagues and include a short note with key takeaways and reminders for the firm.
- Update the firm on its own cybersecurity successes. Make it clear that cyberattacks happen extremely close to home by sharing your firm’s data internally. How many phishing emails were quarantined? How many did not get through firm firewalls? Which staff members should be applauded for calling attention to suspicious activity? At weekly team debriefings or monthly staff meetings, share the statistics that will make a meaningful impression.
- Share key learnings from industry events. At the next advisor conference or other networking event, attend at least one session on cybersecurity. Take copious notes and report back on the main takeaways for keeping the firm protected from thieves.
- Weave cybersecurity into client conversations and new business pitches. Clients may not choose a RIA because of its cybersecurity protocols, but they will certainly leave one if there has been a breach or if they feel their assets and information have been compromised. Take time to explain the firm’s cybersecurity investments and policies and why they are a benefit to clients, and periodically update clients on the firm’s efforts.
- Show clients that cybersecurity matters to the firm. Whether clients visit the office, call in, or advisors meet them offsite, let them experience the team doing extra logins for security, and taking extra steps for identification over the telephone.
- Insist on dumbed-down devices. It is possible to use one mobile device for work and personal matters, and in so doing keep firm and client data secure. Doing so means relinquishing the concept of a “smart phone” and instead giving users mobile devices that only have one work application — the one that gets the user to the firm’s protected smart platform through a multi-factor authentication. Once on the platform, the user can get to any application they need through a centrally managed password vault.
- Consider bringing in outside experts for education. RIA leaders do not have to become experts on cybersecurity in order to guide their firms. Invite the firm’s technology partners to speak at the next offsite or planning meeting, or sign the firm up to attend a webinar.
- Be regulator ready. Industry regulators are paying increasing attention to cybersecurity policies and enforcement, and want to see that firms are taking a more active stance against potential breaches. Set the standard for RIA security by instituting a systematic and replicable ongoing awareness-training program for all advisors and staffers.
Clients entrust RIAs with an awesome and serious task: Their advisors are managing hard-earned assets to achieve very personal life goals. The magnitude of this responsibility should give advisors pause and consider: As part of my mandate, is my firm taking the necessary preventative measures to ensure that our clients are protected from cyberthieves?

Protect Your Firm’s Future: E-Guide on Cybersecurity and Managed IT for RIAs

Year-End Housekeeping for Accountants

Tax Season Readiness: Implementing the Security Six for CPA Firms

How CPA Firms Can Prepare for the Busy Tax Season