The hallmark of the Visory experience, our dedicated team of professionals provides a high degree of support for all your IT needs
Leading edge solutions that are always working to maintain the integrity of your firm’s IT backbone
Best in class security to protect your firm’s data and technology
Tips, advice, and industry insight from our team of accountants and business owners to yours.
Bypass the wait time and access Visory’s Obsessive Client Support®
Take your business to new heights with Visory’s flexible QuickBooks hosting solutions
The same Sage you work in every day, only better
An affordable CRM for small- and medium-sized businesses, built to support your sales, marketing and customer service needs
Revolutionize your next tax season with added efficiency and mobility
Access critical applications that are integrated seamlessly into your workflow, conveniently hosted on the same server
Access affordable enterprise-grade hosting solutions with none of the IT burden

We’ll help you develop and implement the right cybersecurity policies and protocols to keep your firm secure and in compliance with regulatory guidance
We’re here to manage your firm’s IT activity, safeguarding the integrity of your infrastructure and devices, so you don’t have to
Our dedicated professionals can be your outsourced IT team, so your internal resources don’t have to bear the burden of uptime alone.
We’ll manage your cybersecurity policies and protocols to keep your firm secure and in compliance
Security that ensures everyone granted access is who they claim to be
Educate and train your most important last line of defense – your people
Protection where people and their machines intersect
Secure access to your data. Reduce the risk of compromise, prevent cyberthreats.
A different approach to protecting emails
Secure single sign-on access for a connected world
Backup your data for business continuity and compliance
Keep everyone on the same page. Any user, every device.
Secure connections for all your users, devices and networks
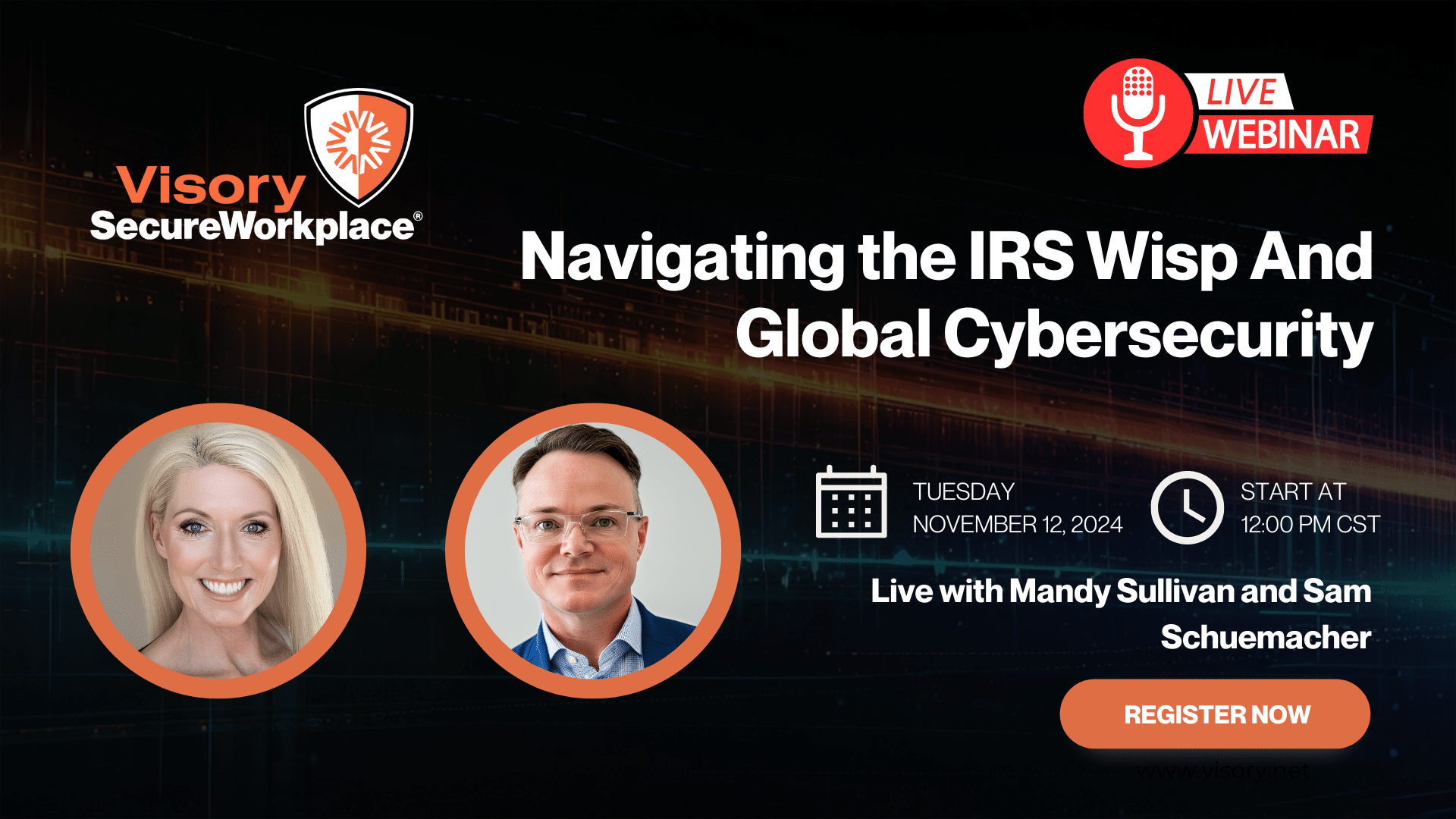
Get started on a robust security plan with a WISP for your business
Protect your organization with the expertise of our Chief Information Security Officers (CISO) without having to hire a full-time resource

IRS 4557 and the FTC Safeguards Rule
Complying with state and federal privacy regulations and more
Get started on a robust security plan with a WISP for your business
Educate and train your most important last line of defense — your people.
Protect your organization with the expertise of our Chief Information Security Officers (CISO) without having to hire a full-time resource
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
Small RIAs are more susceptible to cyberattacks than their owners would like to believe. In fact, with smaller technology budgets and insufficient controls, small firms may be the perfect targets for hackers.
According to a recent report by Symantec on Internet security, personal financial information was the second most common form of data stolen in 2016, behind personally identifiable information.
Implementing and enforcing cybersecurity measures properly should not break the bank. Even without deep pockets to invest in cybersecurity, RIAs should have policies and measures in place to prevent fraud. There are plenty of bells and whistles to choose from, which can make it hard for an advisor to discern what is really necessary. To help, here are six basic elements that should be the foundation for every small RIA’s cybersecurity program.
Use Password Vaults
Passcards hold the authentication credentials to access specific applications and automatically log the user into their assigned applications. Password vaults are a secure solution for storing passcards for RIAs of any size. Typically, there is a master password that grants access to all of the passcards in the vault.
A word of caution: when firms allow employees to create their own passcards, they give them the credentials to access the applications without the use of the vault. This means anyone with credentials can log into applications on unprotected or virus-infected devices, such as personal devices, increasing the risk of a breach. This is typically more problematic for smaller RIAs, which are more likely to lack a chief compliance officer and may neglect compliance.
Firm owners can enforce secure access by creating passcards for all employees for all business-based applications. This virtually eliminates the possibility that others have access to core business applications outside of the password vault and secure devices.
Adopt Two-Factor Authentication
Two-factor authentication is quickly becoming the standard for secure logins. Whereas the password is “the thing you know,” authentication is “the thing you have.” This typically means receiving codes on an authorized device such as a mobile phone or responding to additional prompts to authenticate your login.
Advisors who utilize password vaults and two-factor authentication give their firms quite a bit of cybersecurity protection, even if they do nothing else to guard against potential fraud.

Protect Your Firm’s Future: E-Guide on Cybersecurity and Managed IT for RIAs

Year-End Housekeeping for Accountants

Tax Season Readiness: Implementing the Security Six for CPA Firms

How CPA Firms Can Prepare for the Busy Tax Season