The hallmark of the Visory experience, our dedicated team of professionals provides a high degree of support for all your IT needs
Leading edge solutions that are always working to maintain the integrity of your firm’s IT backbone
Best in class security to protect your firm’s data and technology
Tips, advice, and industry insight from our team of accountants and business owners to yours.
Bypass the wait time and access Visory’s Obsessive Client Support®
Take your business to new heights with Visory’s flexible QuickBooks hosting solutions
The same Sage you work in every day, only better
An affordable CRM for small- and medium-sized businesses, built to support your sales, marketing and customer service needs
Revolutionize your next tax season with added efficiency and mobility
Access critical applications that are integrated seamlessly into your workflow, conveniently hosted on the same server
Access affordable enterprise-grade hosting solutions with none of the IT burden

We’ll help you develop and implement the right cybersecurity policies and protocols to keep your firm secure and in compliance with regulatory guidance
We’re here to manage your firm’s IT activity, safeguarding the integrity of your infrastructure and devices, so you don’t have to
Our dedicated professionals can be your outsourced IT team, so your internal resources don’t have to bear the burden of uptime alone.
We’ll manage your cybersecurity policies and protocols to keep your firm secure and in compliance
Security that ensures everyone granted access is who they claim to be
Educate and train your most important last line of defense – your people
Protection where people and their machines intersect
Secure access to your data. Reduce the risk of compromise, prevent cyberthreats.
A different approach to protecting emails
Secure single sign-on access for a connected world
Backup your data for business continuity and compliance
Keep everyone on the same page. Any user, every device.
Secure connections for all your users, devices and networks
Get started on a robust security plan with a WISP for your business
Protect your organization with the expertise of our Chief Information Security Officers (CISO) without having to hire a full-time resource

IRS 4557 and the FTC Safeguards Rule
Complying with state and federal privacy regulations and more
Get started on a robust security plan with a WISP for your business
Educate and train your most important last line of defense — your people.
Protect your organization with the expertise of our Chief Information Security Officers (CISO) without having to hire a full-time resource
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
You can’t miss the news – new cybersecurity rules for advisors are coming. Though the Securities Exchange Commission (SEC) and others have issued guidance and best practices on cybersecurity for some time, registered investment advisers (RIAs) and funds will now be held accountable for complying with updated rules for protecting against cybersecurity threats and attacks.
The SEC’s proposed new rules and amendments under the Investment Advisers Act of 1940 and the Investment Company Act, focus on risk management, reporting, disclosures and recordkeeping.
Though the comment period for the proposed amendments is still open, advisors should take stock of what will likely be required now to ensure that their cybersecurity protocols and procedures measure up. Not sure how to assess whether your current cybersecurity oversight and preventative measures pass the test? Our downloadable checklist – summarized below – can help you get started:
Visory’s SEC Cybersecurity Readiness Checklist – Does Your RIA Check All These Boxes?
Written cybersecurity plans, policies and procedures. The SEC expects RIAs to review and formalize their cybersecurity risk plans, policies and procedures. This means firms must have written documents that detail workflows and responsibilities and that are clear to all employees.
Policies and procedures for data access management. The SEC is very clear that it wants firms to have detailed Acceptable Use Policy (AUP) documents in place. Who has access to your data, how is it classified and who controls this access? Firms will need to put into place protections like multifactor authentication (MFA), least-privilege access rights and zero-trust monitoring of end devices to comply with the forthcoming new rules.
Protection for data and information. Data must be protected at rest and when in motion, so RIAs will need appropriate technologies and management for keeping information secure at all times. This means relying on things like encryption, threat detection and prevention and mobile device management — technologies that can address their vulnerabilities.
Continuous monitoring. The SEC says it will require advisors “…to have measures to detect, respond to and recover from a cybersecurity incident.” It is expecting that RIAs will continuously monitor their environments for threats and vulnerabilities. Now is the time for firms to consider integrated platforms that can do just that – monitor, alert, respond to and remediate cybersecurity attacks.
Incident response planning and recovery. Every RIA will need a documented incident response plan it can point to in the event of a cyberattack. The plan should be tested for effectiveness and speed of recovery, with gaps addressed to assure business continuity in the event of a significant incident or breach, regardless of where the firm’s data resides.
Reporting and disclosure. The new rule makes very clear that RIAs are on the hook for reporting significant cyber events to the SEC within a relatively short period of time. The Form ADV-C filing requirement means that qualifying incidents must be reported within 48 hours. There are now additional sections on Form AV Part 2A where advisors are required to disclose significant cybersecurity risks and incidents, going back two fiscal years.
Formal accountability. Firms need to identify and establish the internal team responsible and accountable for managing cybersecurity risk. In addition, the firm’s board of directors is now accountable for understanding and addressing the firm’s cybersecurity threats and must approve its cybersecurity policies and procedures. Key point: regardless of whether they outsource cybersecurity, firms are still responsible for that oversight.
Feeling a bit overwhelmed? Don’t be. Over the next several months, we’ll continue to share content and advice from our inhouse technology and cybersecurity experts on exactly what your firm should be doing and how to educate employees to be best prepared.
In the meantime, reach out to us with your questions. We know that keeping up with the demands of the ever-evolving world of technology and cybersecurity while trying to run your RIA and serve clients can be a challenge. That’s why we make it our specialty – so you don’t have to. We are here to partner with you on cybersecurity management today, not just when the SEC shows up.
Need help with your cybersecurity policy? Visory’s RIA consultants can get you on the right track. Fill out our form below to get started.
WM Schedule a meeting
WM LP form
Compliance
Our team of professionals has the right expertise to ensure your technology and cybersecurity complies with the strictest guidance and passes regulatory muster.
Cybersecurity Solutions and Services
Active monitoring and implementation of cybersecurity protocols and procedures using leading edge technology keeps your business and your data safe and secure.

How CPA Firms Can Prepare for the Busy Tax Season
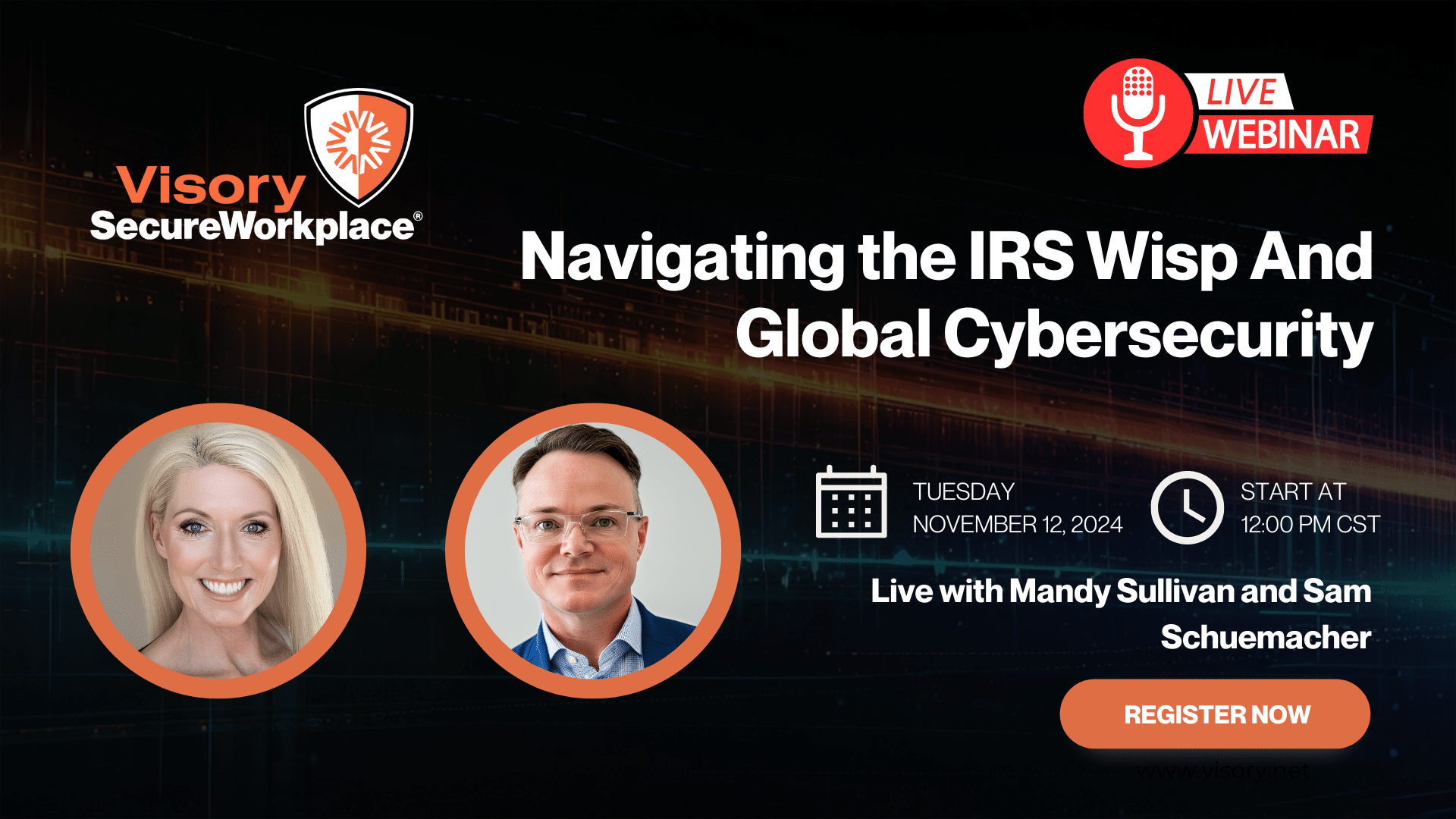
Navigating the IRS WISP and Global Cybersecurity

Cybersecurity for RIAs: Navigating a Shifting Landscape Unaffected by Election Outcomes

Data Breach Survival Guide for Accountants





