The hallmark of the Visory experience, our dedicated team of professionals provides a high degree of support for all your IT needs
Leading edge solutions that are always working to maintain the integrity of your firm’s IT backbone
Best in class security to protect your firm’s data and technology
Tips, advice, and industry insight from our team of accountants and business owners to yours.
Bypass the wait time and access Visory’s Obsessive Client Support®
Take your business to new heights with Visory’s flexible QuickBooks hosting solutions
The same Sage you work in every day, only better
An affordable CRM for small- and medium-sized businesses, built to support your sales, marketing and customer service needs
Revolutionize your next tax season with added efficiency and mobility
Access critical applications that are integrated seamlessly into your workflow, conveniently hosted on the same server
Access affordable enterprise-grade hosting solutions with none of the IT burden

We’ll help you develop and implement the right cybersecurity policies and protocols to keep your firm secure and in compliance with regulatory guidance
We’re here to manage your firm’s IT activity, safeguarding the integrity of your infrastructure and devices, so you don’t have to
Our dedicated professionals can be your outsourced IT team, so your internal resources don’t have to bear the burden of uptime alone.
We’ll manage your cybersecurity policies and protocols to keep your firm secure and in compliance
Security that ensures everyone granted access is who they claim to be
Educate and train your most important last line of defense – your people
Protection where people and their machines intersect
Secure access to your data. Reduce the risk of compromise, prevent cyberthreats.
A different approach to protecting emails
Secure single sign-on access for a connected world
Backup your data for business continuity and compliance
Keep everyone on the same page. Any user, every device.
Secure connections for all your users, devices and networks
Get started on a robust security plan with a WISP for your business
Protect your organization with the expertise of our Chief Information Security Officers (CISO) without having to hire a full-time resource

IRS 4557 and the FTC Safeguards Rule
Complying with state and federal privacy regulations and more
Get started on a robust security plan with a WISP for your business
Educate and train your most important last line of defense — your people.
Protect your organization with the expertise of our Chief Information Security Officers (CISO) without having to hire a full-time resource
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
In our interconnected digital world, the security of digital communications is more important than ever. Business email compromise (BEC) has emerged as a sophisticated scam targeting companies across various industries. It exploits the very fabric of communication channels by illegally accessing and manipulating business email accounts, posing a severe threat to the integrity and financial health of businesses globally.
91% of all cyberattacks start with an email, and recent data recorded in Mimecast’s seventh annual State of Email Security Report stated that 75% of businesses have seen an increase in email-based threats. This growth is a top security concern for businesses of all sizes, as cybercriminals have found various ways to breach business email protocols and cause significant financial and reputational damage. Visory aims to prepare you for these insidious threats and help safeguard your company from business email compromise.
What is Business Email Compromise?
Business email compromise (BEC) is a type of cyberattack that uses email to trick someone into sending money or sharing confidential information. As remote work becomes more prevalent, the risk of BEC scams increases, making robust cybersecurity critical for businesses that offer hybrid or remote working options. The FBI has identified 5 primary types of BEC attacks:
- CEO Fraud: To gain the victim’s trust and potentially funds, attackers pose as the CEO or executive of your company and email individuals in the finance department requesting a money transfer of some kind.
- Account Compromise: In this scenario, an individual employee’s email is hacked and used to request vendor payments. These funds are then sent to fraudulent bank accounts controlled by the attacker.
- Attorney Impersonation: An attacker may impersonate a lawyer, attorney, or other legal representative to gain information or payment. These types of scams often target lower-level employees who may not have the knowledge to question the request’s validity or the sender’s identity.
- Fake Invoice: Foreign suppliers are often targeted by this BEC tactic, in which the scammer pretends they are the supplier and request money transfers to fake accounts.
- Data Theft: Instead of requesting money, attackers using data theft methods attempt to trick recipients into revealing confidential personal or company information. This type of BEC is typically targeted at HR employees to try and gain information about company executives and other employees.
How do BEC Scams Happen?
While there are many types of BEC scams, all attackers pose as a person the recipient can trust, commonly a co-worker, boss, or vendor. This requires extensive research ahead of time, and in some cases, attackers will create fake websites or register companies with the same name in a different country to support the illusion.
Once the attackers gain access to your systems, they monitor email activity to decide which individual to specifically target and how likely they are to send funds. This is when they will send their first communication, working to gain the victim’s trust before asking for money and/or information. It is common for scammers to spoof your company email domain while communicating with victims.
Some of the most common initial requests from scammers are:
- Pay this urgent bill.
- Re-confirm your phone number.
- A lease is expiring.
- A secret business deal.
How to Protect Your Business from Business Email Compromise
BEC scams can significantly impact your business, making it essential to implement robust preventative strategies that can effectively protect your employees, funds, and data. A cybersecurity expert like Visory can help you create advanced protective protocols and can monitor your network for additional security.
Employee Training and Awareness
The first line of defense against BEC is a well-informed workforce. First and foremost, encourage your team to always be suspicious. If something seems off, asking for clarification, forwarding the email to your IT department, or checking with a co-worker is better than agreeing to the request outright. Additionally, remind your employees to trust their instincts. If the request doesn’t seem right, ask questions like, “Would my CEO really ask me to do this?” Even if the answer is yes, it’s always best to check with others on your team before submitting the request.
Lastly, train your team to slow down. BEC scammers typically send their emails during the busiest periods of the day to take advantage of your lack of free time. By reading your emails and clearing your inbox more carefully, you lower the chance of accidentally communicating with an attacker.
To reinforce your training, you can also conduct simulated BEC attacks. These exercises test your employees’ ability to recognize and respond to fake BEC scenarios, enhancing their vigilance and ensuring they’re prepared for real-life situations.
Comprehensive Security Protocols
To ward off potential BEC scams, you should implement robust security measures. Multi-factor authentication (MFA) is a great place to start, as it adds a layer of security to your accounts. This makes it more challenging for scammers to gain unauthorized access to email accounts, even with compromised credentials.
You can also utilize sophisticated email filtering systems to detect and block suspicious emails. These systems should be capable of analyzing email content for signs of BEC, such as unusual requests or changes in bank account details. Regular monitoring for abnormal email activity is critical in the early detection of BEC attempts.
Policy Development and Enforcement
Alongside effective cybersecurity protocols, you should establish and enforce clear policies regarding email communications, especially concerning financial transactions and sensitive information. This includes verifying changes in payment details with known contacts through a secondary communication channel.
Once these policies are in place, periodically review and update them to ensure they remain effective against evolving BEC tactics. Audits can help you identify potential vulnerabilities and areas for improvement in your organization’s email security practices.
Incident Response Plan
Even with the most advanced and trusted security measures in place, your company could still be targeted by a BEC scam. Having a well-defined plan for responding to BEC incidents can help you reduce the impact of an attack. This plan should include steps for containment, eradication, and recovery, as well as protocols for reporting the incident to relevant authorities. Regularly test and update your incident response plan to ensure its effectiveness in the face of new types of BEC attacks.
Safeguard Against Cyberattacks with Visory
BEC attacks are continually evolving, making it essential for businesses of all sizes to stay informed about the latest tactics used by cybercriminals. Beyond staying vigilant, the best way to protect against business email compromise is to work with an expert cybersecurity firm that can develop and implement the most effective strategies for your unique needs.
Visory offers tailored solutions to specifically address the vulnerabilities and requirements of your organization. Our team of experts is dedicated to ensuring your business is prepared to tackle current threats and equipped to face future challenges in the digital landscape.
Learn more about our cybersecurity solutions and how we can secure your business against the unpredictable. To start a conversation about your cybersecurity needs, contact a Visory expert today.

How CPA Firms Can Prepare for the Busy Tax Season
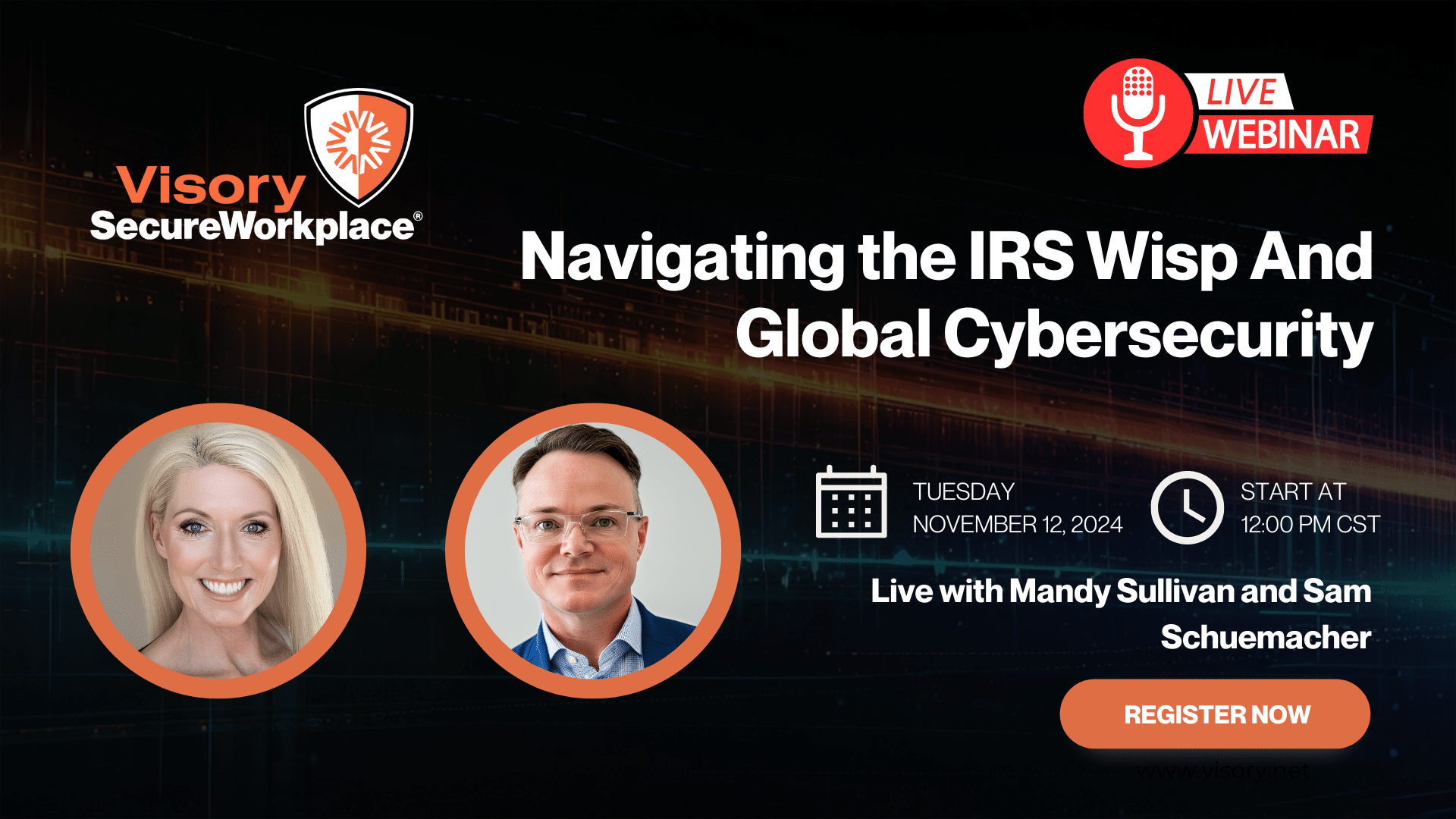
Navigating the IRS WISP and Global Cybersecurity

Cybersecurity for RIAs: Navigating a Shifting Landscape Unaffected by Election Outcomes

Data Breach Survival Guide for Accountants





