The hallmark of the Visory experience, our dedicated team of professionals provides a high degree of support for all your IT needs
Leading edge solutions that are always working to maintain the integrity of your firm’s IT backbone
Best in class security to protect your firm’s data and technology
Tips, advice, and industry insight from our team of accountants and business owners to yours.
Bypass the wait time and access Visory’s Obsessive Client Support®
Take your business to new heights with Visory’s flexible QuickBooks hosting solutions
The same Sage you work in every day, only better
An affordable CRM for small- and medium-sized businesses, built to support your sales, marketing and customer service needs
Revolutionize your next tax season with added efficiency and mobility
Access critical applications that are integrated seamlessly into your workflow, conveniently hosted on the same server
Access affordable enterprise-grade hosting solutions with none of the IT burden

We’ll help you develop and implement the right cybersecurity policies and protocols to keep your firm secure and in compliance with regulatory guidance
We’re here to manage your firm’s IT activity, safeguarding the integrity of your infrastructure and devices, so you don’t have to
Our dedicated professionals can be your outsourced IT team, so your internal resources don’t have to bear the burden of uptime alone.
We’ll manage your cybersecurity policies and protocols to keep your firm secure and in compliance
Security that ensures everyone granted access is who they claim to be
Educate and train your most important last line of defense – your people
Protection where people and their machines intersect
Secure access to your data. Reduce the risk of compromise, prevent cyberthreats.
A different approach to protecting emails
Secure single sign-on access for a connected world
Backup your data for business continuity and compliance
Keep everyone on the same page. Any user, every device.
Secure connections for all your users, devices and networks
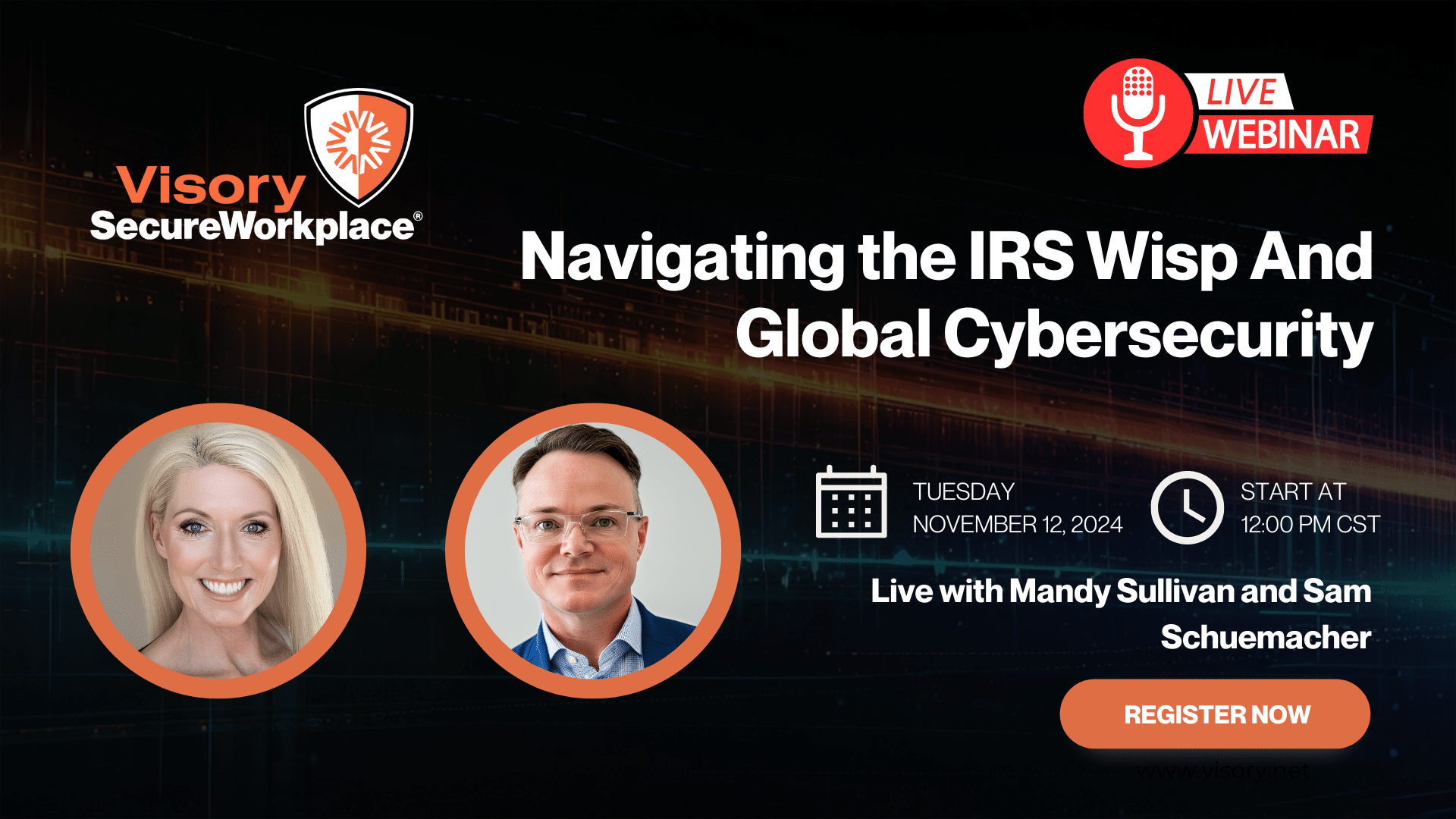
Get started on a robust security plan with a WISP for your business
Protect your organization with the expertise of our Chief Information Security Officers (CISO) without having to hire a full-time resource

IRS 4557 and the FTC Safeguards Rule
Complying with state and federal privacy regulations and more
Get started on a robust security plan with a WISP for your business
Educate and train your most important last line of defense — your people.
Protect your organization with the expertise of our Chief Information Security Officers (CISO) without having to hire a full-time resource
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
In the evolving landscape of cyber threats, businesses must protect themselves from zero-day attacks. These attacks strike the core of your business operations, targeting the tools and systems you rely on daily. Understanding the nature of zero-day attacks isn’t just about keeping your data safe; it’s about preserving the integrity and trust in your services and products.
What is a Zero-Day Attack?
Zero-day attacks and exploits are not your average cyber threats; they are “must-fix” issues that arise when hackers discover and exploit a vulnerability in your software or system to steal data, plant malware, or cause damage to users, systems, and organizations. Hackers find and leverage a weakness in your system before anyone is aware of its existence, giving developers zero days to address the issue and coining the name “zero-day” attack.
According to an analysis completed by Mandiant, 55 zero-day vulnerabilities were exploited in 2022. While 81 zero-day attacks occurred in 2021, the number of exploits in 2022 was still significantly higher than in 2020 and previous years. Mandiant experts predict that zero-day attacks will happen more frequently as the number of exploited vulnerabilities grows yearly.
How Do Zero-Day Attacks Happen?
Understanding how zero-day attacks occur is critical to defending yourself against one. Here is a breakdown of how many of these cyber assaults unfold:
- Discovery of the Flaw: The attack begins when a hacker identifies a vulnerability in your system or software, known as a zero-day vulnerability. In the best-case scenario, your security team discovers this weak spot first, but zero-day vulnerabilities are often unknown to developers and users alike and may lie dormant in widely used software, operating systems, and web applications.
- Creating the Exploit: The attackers create an exploit once the vulnerability is exposed. Exploits can take the form of malicious code or instructions specifically designed to leverage the weakness they’ve uncovered.
- Execution: With the exploit planned and created, the hackers find a vector for delivery. It could be a simple phishing email, a complete hijacking of legitimate websites to serve malware, or a direct exploit of network services. The attacker’s goal may be to steal sensitive data, gain unauthorized access to systems, or plant malware that can cause long-term damage.
- Concealment: As the exploit works, the attackers employ techniques to obscure their activities, making it difficult for users or security systems to detect or identify the hackers.
Not all zero-day attacks are the same; they can range from limited strikes on individual targets to widespread campaigns against large networks. Recognizing the variance in zero-day attacks allows you to create an adaptable and robust cybersecurity strategy to minimize the threat.
How Do You Respond to a Zero-Day Exploit?
Quickly responding to a suspected zero-day exploit can make a significant difference in its impact on your organization. When a zero-day attack occurs, here are a few key actions to take:
- Isolate Affected Systems: Immediately quarantine or isolate the affected system or software at the first hint of an attack. This containment is critical to prevent the attack from spreading across the network and potentially reaching other systems or data stores.
- Form a Response Team: Once you’ve isolated the systems under attack, assemble a team of experts to uncover the attack’s origin, understand its scope, and assess its impact. Your response team should scrutinize why and how the breach occurred to try and close any security gaps and strengthen your defenses.
- Prioritize Communication: Clear communication with your internal team is essential, and it’s critical to inform relevant departments of the breach as quickly as possible. Beyond creating a united front against the attack, communicating well within your company allows individuals to take protective measures against the attack and support the containment and recovery efforts. Equally important is how you share the information with external parties. At the same time, you shouldn’t disclose any sensitive information that could worsen the situation, and it is important to inform customers, partners, and stakeholders of the breach.
- Develop a Solution: While searching for the cause of the breach and the hackers behind it, there should be a concentrated effort to develop a fix. Whether the solution is an in-house generated patch or one created by a trusted third-party vendor, it should effectively neutralize the exploit and restore the integrity of affected systems.
- Test the Fix: Before the patch or solution can be widely deployed, you must complete rigorous testing to ensure it addresses the zero-day vulnerability without introducing new issues into the system.
What Happens Next?
In the aftermath of a zero-day attack, your actions are critical in securing your systems against future exploits. Once the immediate threat is neutralized and the affected systems are restored, you should constantly monitor the network traffic and system logs to resolve the issue entirely. Stay on the lookout for any anomalies that could suggest the presence of backdoors or secondary payloads left by the attacker, which they could use to regain access or launch another attack.
After the attack, your company may want to reevaluate security protocols and policies for potential future incidents. Depending on your team’s experience, you may also want to hire a cybersecurity expert like Visory to offer advanced protection services and advice.
What Can Your Company Do to Mitigate the Risk of a Zero-Day Attack?
Keep All Software and Cybersecurity Updated
The first line of defense against zero-day attacks is maintaining a strict update protocol. Every software, operating system, and component in your digital infrastructure should be patched with the latest security updates as soon as they become available to minimize the window of opportunity for hackers.
Also, ensure your company stays aware of cybersecurity trends and changes. Hackers constantly evolve, so you can anticipate and prepare for potential vulnerabilities by understanding the current environment and threats.
Educate Your Employees
Human error remains one of the biggest security vulnerabilities in any organization. Regular and comprehensive cybersecurity training for all employees is critical to the overall security of your network. Your employees need to learn how to recognize potential threats, like sophisticated phishing attempts, to reduce the chance of human error contributing to a zero-day attack.
Utilize Detection Systems
To further protect your systems from zero-day attacks, you can deploy an advanced detection system, such as an intrusion detection system (IDS), to spot unusual activities that could signal an impending exploit. Intrusion detection systems also provide the necessary intel to respond to an attack early, which can significantly mitigate the impact of the breach.
Visory is Here to Help Your Company Stay Safe
Zero-day attacks pose a significant threat to businesses in the ever-changing digital landscape. While these attacks cannot be entirely prevented, updating your defense mechanisms and having a dedicated business IT support partner can help you avoid a zero-day exploit.
At Visory, we understand that the best defense against the unknown is a security team you can trust. That’s why we provide small and medium businesses with IT solutions that protect your organization and users from cyber attacks. Our experts work tirelessly to continuously update your systems, monitor your network, and educate your staff.
Learn more about our cybersecurity solutions and how we can secure your business against the unpredictable. To start a conversation about your cybersecurity needs, contact a Visory expert today.
Cybersecurity Solutions and Services
Active monitoring and implementation of cybersecurity protocols and procedures using leading edge technology keeps your business and your data safe and secure.
Managed Services
Rely on our industry expertise to reduce your IT burden and access the best technology solution to help your business grow.
Protect Your Firm from Data Risks

Protect Your Firm’s Future: E-Guide on Cybersecurity and Managed IT for RIAs

Year-End Housekeeping for Accountants

Tax Season Readiness: Implementing the Security Six for CPA Firms