The hallmark of the Visory experience, our dedicated team of professionals provides a high degree of support for all your IT needs
Leading edge solutions that are always working to maintain the integrity of your firm’s IT backbone
Best in class security to protect your firm’s data and technology
Tips, advice, and industry insight from our team of accountants and business owners to yours.
Bypass the wait time and access Visory’s Obsessive Client Support®
Take your business to new heights with Visory’s flexible QuickBooks hosting solutions
The same Sage you work in every day, only better
An affordable CRM for small- and medium-sized businesses, built to support your sales, marketing and customer service needs
Revolutionize your next tax season with added efficiency and mobility
Access critical applications that are integrated seamlessly into your workflow, conveniently hosted on the same server
Access affordable enterprise-grade hosting solutions with none of the IT burden

We’ll help you develop and implement the right cybersecurity policies and protocols to keep your firm secure and in compliance with regulatory guidance
We’re here to manage your firm’s IT activity, safeguarding the integrity of your infrastructure and devices, so you don’t have to
Our dedicated professionals can be your outsourced IT team, so your internal resources don’t have to bear the burden of uptime alone.
We’ll manage your cybersecurity policies and protocols to keep your firm secure and in compliance
Security that ensures everyone granted access is who they claim to be
Educate and train your most important last line of defense – your people
Protection where people and their machines intersect
Secure access to your data. Reduce the risk of compromise, prevent cyberthreats.
A different approach to protecting emails
Secure single sign-on access for a connected world
Backup your data for business continuity and compliance
Keep everyone on the same page. Any user, every device.
Secure connections for all your users, devices and networks
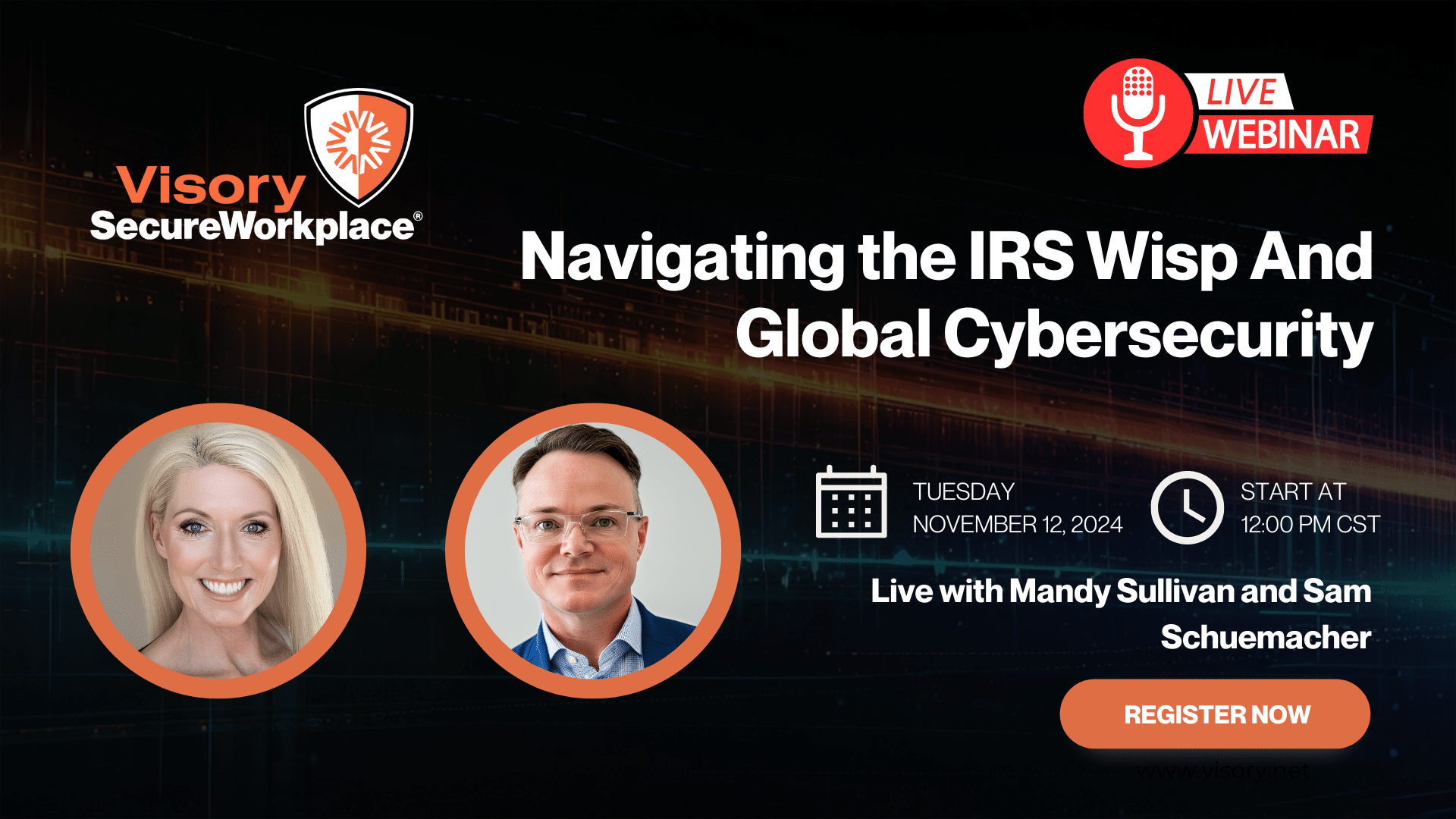
Get started on a robust security plan with a WISP for your business
Protect your organization with the expertise of our Chief Information Security Officers (CISO) without having to hire a full-time resource

IRS 4557 and the FTC Safeguards Rule
Complying with state and federal privacy regulations and more
Get started on a robust security plan with a WISP for your business
Educate and train your most important last line of defense — your people.
Protect your organization with the expertise of our Chief Information Security Officers (CISO) without having to hire a full-time resource
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy

In case you hadn’t heard, the Securities and Exchange Commission recently fined eight financial firms a total of $750,000 over email hacks that exposed client data. The SEC found that the firms had inadequate cybersecurity protections, which led to the exposure of personally identifiable information of thousands of customers and clients after hackers took over employee email accounts.
Despite what their own cybersecurity policies mandated, these firms did not have multifactor authentication (MFA) in place. The SEC found these firms in violation of the “Safeguards Rule,” more formally known as Rule 30(a) of Regulation S-P, which is designed to protect confidential customer information.
Ouch. As we’ve said before, it is not enough to have a cybersecurity policy, the policy must be implemented, actively monitored, and enforced in order for it to be defendable (and for the firm to stay protected).
Ironically, we chose to address the importance of MFA in our August Tech Trends blog Ransomware Attacks Are Closer Than You Think. Given recent headlines, we thought it was important to reiterate the best practices for staying secure:
- Implement adaptive MFA and end device management – used in combination, these tools can prevent most cybersecurity attacks.
- Don’t click on any links or attachments inside phishing emails. Doing so instantly compromises the email account and puts the firm’s IT network into the hands of a criminal or criminal network.
- Never upload or offer your credentials unless you are expecting to access a known system. When in doubt, don’t enter anything in and call your IT support team.
- Have your IT support team implement a cybersecurity training and testing program for your entire organization on data protection and cybersecurity protocols.
- Pay attention to the senders of inbound emails. “Spoofed” email addresses look similar enough to a legitimate address and can trick the unsuspecting receiver into giving away access or information to a cyberthief.
We can’t overstate the importance of keeping your network secure. A hacked system – whether through compromised email or other means – can have severe and even devastating consequences, not only for the firms that are attacked, but for the individuals and families whose personal and financial information ends up in the hands of bad actors.
Compliance
Our team of professionals has the right expertise to ensure your technology and cybersecurity complies with the strictest guidance and passes regulatory muster.
Cybersecurity Solutions and Services
Active monitoring and implementation of cybersecurity protocols and procedures using leading edge technology keeps your business and your data safe and secure.

Protect Your Firm’s Future: E-Guide on Cybersecurity and Managed IT for RIAs

Year-End Housekeeping for Accountants
IRS WISP Compliance Resource Hub

Tax Season Readiness: Implementing the Security Six for CPA Firms