The hallmark of the Visory experience, our dedicated team of professionals provides a high degree of support for all your IT needs
Leading edge solutions that are always working to maintain the integrity of your firm’s IT backbone
Best in class security to protect your firm’s data and technology
Tips, advice, and industry insight from our team of accountants and business owners to yours.
Bypass the wait time and access Visory’s Obsessive Client Support®
Take your business to new heights with Visory’s flexible QuickBooks hosting solutions
The same Sage you work in every day, only better
An affordable CRM for small- and medium-sized businesses, built to support your sales, marketing and customer service needs
Revolutionize your next tax season with added efficiency and mobility
Access critical applications that are integrated seamlessly into your workflow, conveniently hosted on the same server
Access affordable enterprise-grade hosting solutions with none of the IT burden

We’ll help you develop and implement the right cybersecurity policies and protocols to keep your firm secure and in compliance with regulatory guidance
We’re here to manage your firm’s IT activity, safeguarding the integrity of your infrastructure and devices, so you don’t have to
Our dedicated professionals can be your outsourced IT team, so your internal resources don’t have to bear the burden of uptime alone.
We’ll manage your cybersecurity policies and protocols to keep your firm secure and in compliance
Security that ensures everyone granted access is who they claim to be
Educate and train your most important last line of defense – your people
Protection where people and their machines intersect
Secure access to your data. Reduce the risk of compromise, prevent cyberthreats.
A different approach to protecting emails
Secure single sign-on access for a connected world
Backup your data for business continuity and compliance
Keep everyone on the same page. Any user, every device.
Secure connections for all your users, devices and networks
Get started on a robust security plan with a WISP for your business
Protect your organization with the expertise of our Chief Information Security Officers (CISO) without having to hire a full-time resource

IRS 4557 and the FTC Safeguards Rule
Complying with state and federal privacy regulations and more
Get started on a robust security plan with a WISP for your business
Educate and train your most important last line of defense — your people.
Protect your organization with the expertise of our Chief Information Security Officers (CISO) without having to hire a full-time resource
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
In today’s interconnected digital landscape, it’s no longer a matter of if your organization will face a ransomware attack but when. The ever-present threat of ransomware looms large, ready to strike organizations of all sizes. Protecting your digital assets and sensitive information is more important than ever. While the fight against ransomware may sometimes feel like a never-ending game of whack-a-mole, it’s crucial to understand the key avenues that cyber adversaries exploit and take proactive steps to secure your organization.
The Need for Ransomware Prevention
Preventing ransomware events is essential, and it doesn’t require you to become a cybersecurity expert. Just as you have legal or financial advisors for critical business decisions, there are IT and cybersecurity experts who can help you secure your digital environment. The following best practices align with recommendations from the Cybersecurity and Infrastructure Security Agency (CISA) and other cybersecurity experts. Implementing them can significantly reduce the risk of a cyber attack.
Transparency is Key
Understanding your technology environment is the first step to securing it. Document who has access, what is being accessed and when, and where in your technology ecosystem. This transparency allows you to identify potential vulnerabilities and develop a plan to address them throughout your organization.
Keep Software Updated
Cybercriminals often target both new and old vulnerabilities. It’s crucial to stay ahead of potential threats by regularly patching and updating your software and operating systems. By doing so, you prevent adversaries from exploiting known weaknesses.
Control Remote Access
In the wake of the COVID-19 pandemic, remote work has become the norm. However, it’s essential to monitor and secure remote access points. Limit the use of Remote Desktop Services (RDP) and employ strong authentication mechanisms to prevent unauthorized access.
Password Policies Matter
Implement strong password policies that require unique passwords of at least 15 characters. Password managers can assist in creating and managing secure passwords. Ensure your staff understands and adheres to these policies to strengthen your defense.
Educate Against Phishing
Phishing attacks remain a significant threat. Educate your staff about phishing tactics and the importance of cybersecurity controls. Regular reinforcement is key to fostering a security-conscious culture within your organization.
Enable Multi-Factor Authentication (MFA)
Multi-factor authentication enhances security by requiring multiple forms of authentication. It’s a powerful defense against cyber adversaries attempting to impersonate users. Implement MFA across your systems to protect your organization from unauthorized access.
Backup Strategically
While automated cloud backups are valuable, they might not be foolproof. Ransomware attacks could target online backups. Thus, maintaining offline backups of your most critical data is crucial to protect against these attacks.
Have an Incident Response Plan
Prepare for the worst by creating, maintaining, and regularly exercising a cyber incident response plan (IRP). Your team should know how to respond swiftly and effectively in the event of an attack.
Preventing ransomware attacks is a top priority for organizations in today’s digital age. By following these best practices and having a solid response plan in place, you can significantly reduce the risk of falling victim to ransomware. Remember, in the world of cybersecurity, knowledge and preparation are your most potent weapons.

How CPA Firms Can Prepare for the Busy Tax Season
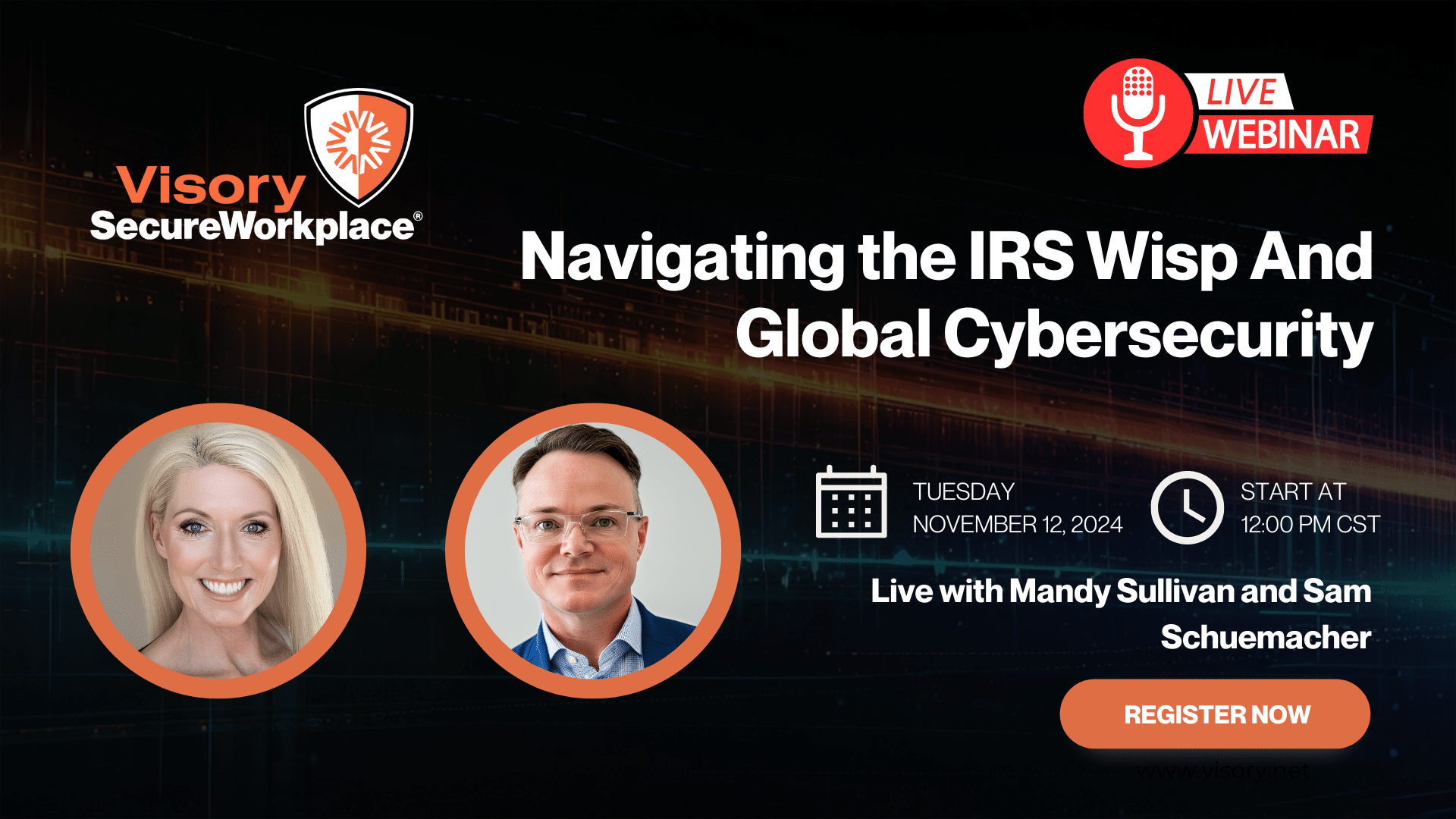
Navigating the IRS WISP and Global Cybersecurity

Cybersecurity for RIAs: Navigating a Shifting Landscape Unaffected by Election Outcomes

Data Breach Survival Guide for Accountants





