The hallmark of the Visory experience, our dedicated team of professionals provides a high degree of support for all your IT needs
Leading edge solutions that are always working to maintain the integrity of your firm’s IT backbone
Best in class security to protect your firm’s data and technology
Tips, advice, and industry insight from our team of accountants and business owners to yours.
Bypass the wait time and access Visory’s Obsessive Client Support®
Take your business to new heights with Visory’s flexible QuickBooks hosting solutions
The same Sage you work in every day, only better
An affordable CRM for small- and medium-sized businesses, built to support your sales, marketing and customer service needs
Revolutionize your next tax season with added efficiency and mobility
Access critical applications that are integrated seamlessly into your workflow, conveniently hosted on the same server
Access affordable enterprise-grade hosting solutions with none of the IT burden

We’ll help you develop and implement the right cybersecurity policies and protocols to keep your firm secure and in compliance with regulatory guidance
We’re here to manage your firm’s IT activity, safeguarding the integrity of your infrastructure and devices, so you don’t have to
Our dedicated professionals can be your outsourced IT team, so your internal resources don’t have to bear the burden of uptime alone.
We’ll manage your cybersecurity policies and protocols to keep your firm secure and in compliance
Security that ensures everyone granted access is who they claim to be
Educate and train your most important last line of defense – your people
Protection where people and their machines intersect
Secure access to your data. Reduce the risk of compromise, prevent cyberthreats.
A different approach to protecting emails
Secure single sign-on access for a connected world
Backup your data for business continuity and compliance
Keep everyone on the same page. Any user, every device.
Secure connections for all your users, devices and networks
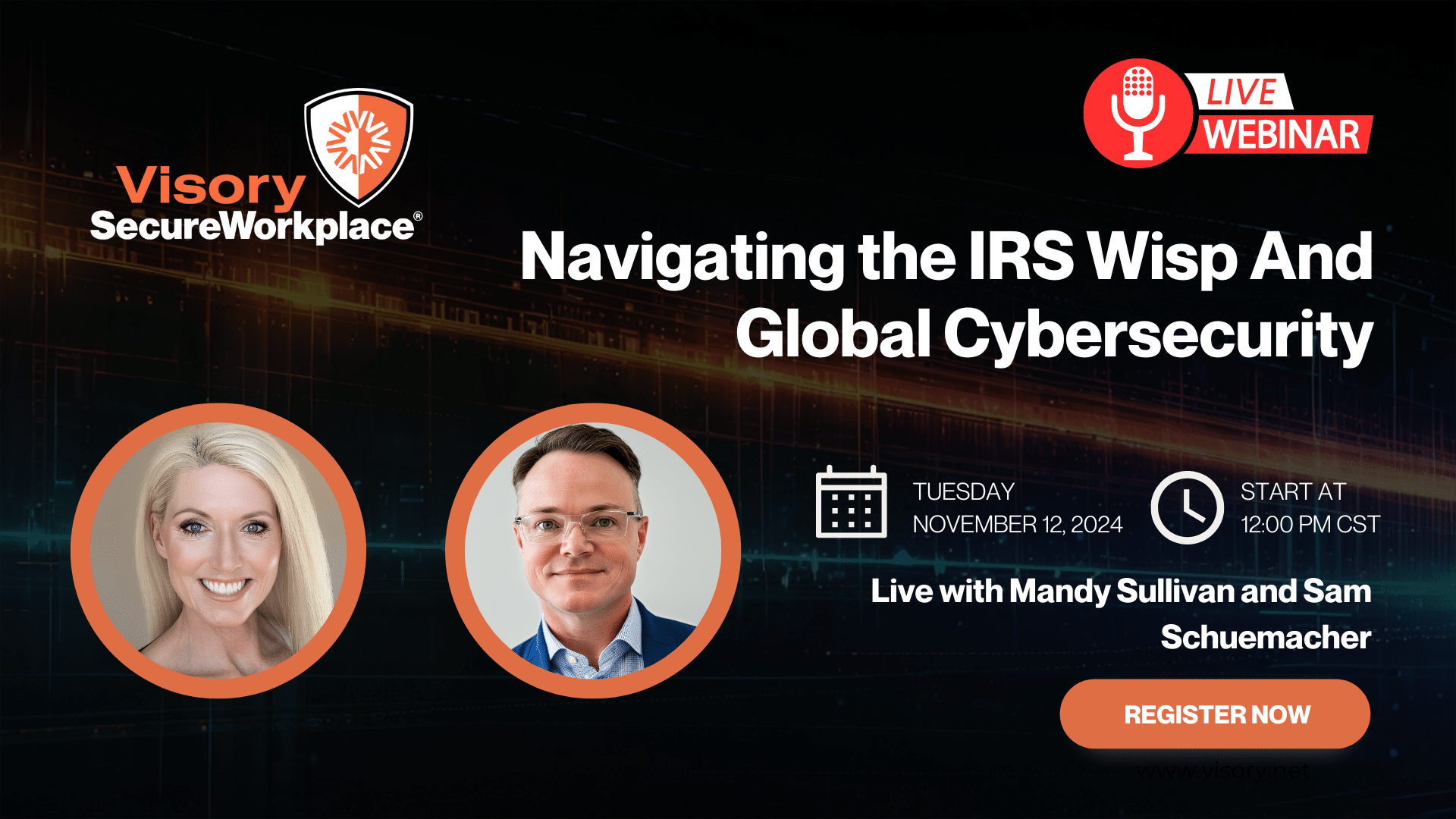
Get started on a robust security plan with a WISP for your business
Protect your organization with the expertise of our Chief Information Security Officers (CISO) without having to hire a full-time resource

IRS 4557 and the FTC Safeguards Rule
Complying with state and federal privacy regulations and more
Get started on a robust security plan with a WISP for your business
Educate and train your most important last line of defense — your people.
Protect your organization with the expertise of our Chief Information Security Officers (CISO) without having to hire a full-time resource
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
The inappropriate use of email can spell disaster for registered investment advisors (RIAs), particularly for firms with multiple offices or remote workers, and for those with employees who use personal devices to transact business.
There are measures that RIAs can take to protect themselves in the event of issues involving indiscriminate email usage or regulatory audits. An email policy is a start, but advisors are best served – and in compliance – when they actively monitor emails and enforce policy.
Email Policy Basics
Those responsible for human resources or in charge of firm management often take the lead in drafting a RIA’s email usage and retention policies, but the strongest policies typically include input from outside experts such as outside legal counsel or information technology (IT) service partners.
At minimum, a good email policy will state that the contents of every email will not breach firm or client confidentiality. The policy should also explicitly explain that any technology-related tools, devices and services owned by the firm are to be used solely for the purpose of transacting business and are not for personal use.
The firm’s email retention policy may also be spelled out. In the event of an audit, RIAs must be able to show that their email policy complies with Rule 204-2 of the Investment Advisers Act, the Books and Records Rule, which requires emails to be retained for five years after the fiscal year they were sent.
All RIA partners and employees should sign and date a written policy when it is presented, with the original being kept by the firm and a copy given to the signatory.
Auditing Emails
Of course, no matter how well written, a firm’s email policy must be enforced to be effective and must stand up to regulatory audits. To comply with SEC regulations, RIAs must be able to prove they are systematically checking emails. Random, periodic assessments of emails will not suffice as the firm’s email audit protocol.
RIAs and their IT professionals should be working with programs or providers to monitor outbound and inbound emails actively, employing a rules-based approach to look for number and word patterns. The auditing process should flag potentially suspicious or undesirable content, including spotting language such as “I guarantee…,” or “I promise…”, and also flag emails containing confidential information. Firms must also be vigilant about blocking inbound email spam, as well as outbound emails to undesirable sites.
Email Encryption
RIAs are on the hook for ensuring that emails are delivered and received correctly, which firms can do through encrypted connections and emails. Encrypting outbound email provides the firm with a receipt to prove that this was done correctly and securely, through an encrypted connection. The encrypted connection also offers the firm protection for inbound emails. RIAs should not limit email encryption to the office; access to the firm email platform should only occur through password-protected and encrypted mobile devices as well.
Mobile Devices and Email
RIAs need to carefully consider how or whether employees access email via personal mobile devices. The chief concern is the ability to encrypt, audit and archive inbound and outbound firm emails, and text messages, from any access point.
There are two best practices for maintaining control over mobile email usage. The first is to limit access to firm email to personal mobile devices that are encrypted and password protected. The usage policy should be explicit: “We will not allow firm email on personal mobile devices unless the devices are equipped with our encryption and password protection programs.” If the employee leaves the firm or loses the device, the firm has the right to wipe the device. Unfortunately, very few RIAs choose this best-in-class practice. Many advisors wrongly believe that this type of policy gives the firm the right to unrestricted access and control of all data on an employee’s personal mobile device. But this is simply not the case – the RIA does not get access to the data on the device. Rather, the entire hard drive is encrypted and the device is password protected to be in compliance with regulatory requirements, and to safeguard the RIA from any potential liability resulting from email usage that falls outside of firm policy.
The second best practice is to use firm-issued mobile devices that are password-protected and encrypted for email. This alternative addresses concerns about privacy, data access and ownership. But resistance to carrying two devices can be very strong. It is more often the case that a RIA may offer firm-issued mobile devices; it is rare to find firms that insist on them.
Archiving Emails
All state- and SEC-registered RIAs should be archiving email, but many are surprised to learn that not all archiving tools pass regulatory muster. In fact, any tool that allows emails to be modified or removed is not a true archive and will not stand up in an audit. This means that the default archive tools in Outlook, Mail and most customer relationship management (CRM) systems are not SEC-compliant archives.
Once armed with tools or providers that will archive email in a SEC-compliant manner, advisors should consider using their archive as a tool to be used their own business purposes. The email archive can be mined and sorted for data, which can compliment the functionality and features of the CRM.
It’s Time to Activate Your Email Policy
RIAs need to safeguard themselves against potential business and reputational damage when events unfold in ways that are outside of their control. Through proper monitoring and enforcement, well-thought-out email usage policies can only help advisors in the event of a crisis or regulatory audit.
Cybersecurity Solutions and Services
Active monitoring and implementation of cybersecurity protocols and procedures using leading edge technology keeps your business and your data safe and secure.
Managed Services
Rely on our industry expertise to reduce your IT burden and access the best technology solution to help your business grow.
Protect Your Firm from Data Risks

Protect Your Firm’s Future: E-Guide on Cybersecurity and Managed IT for RIAs

Year-End Housekeeping for Accountants

Tax Season Readiness: Implementing the Security Six for CPA Firms